SAFECASE
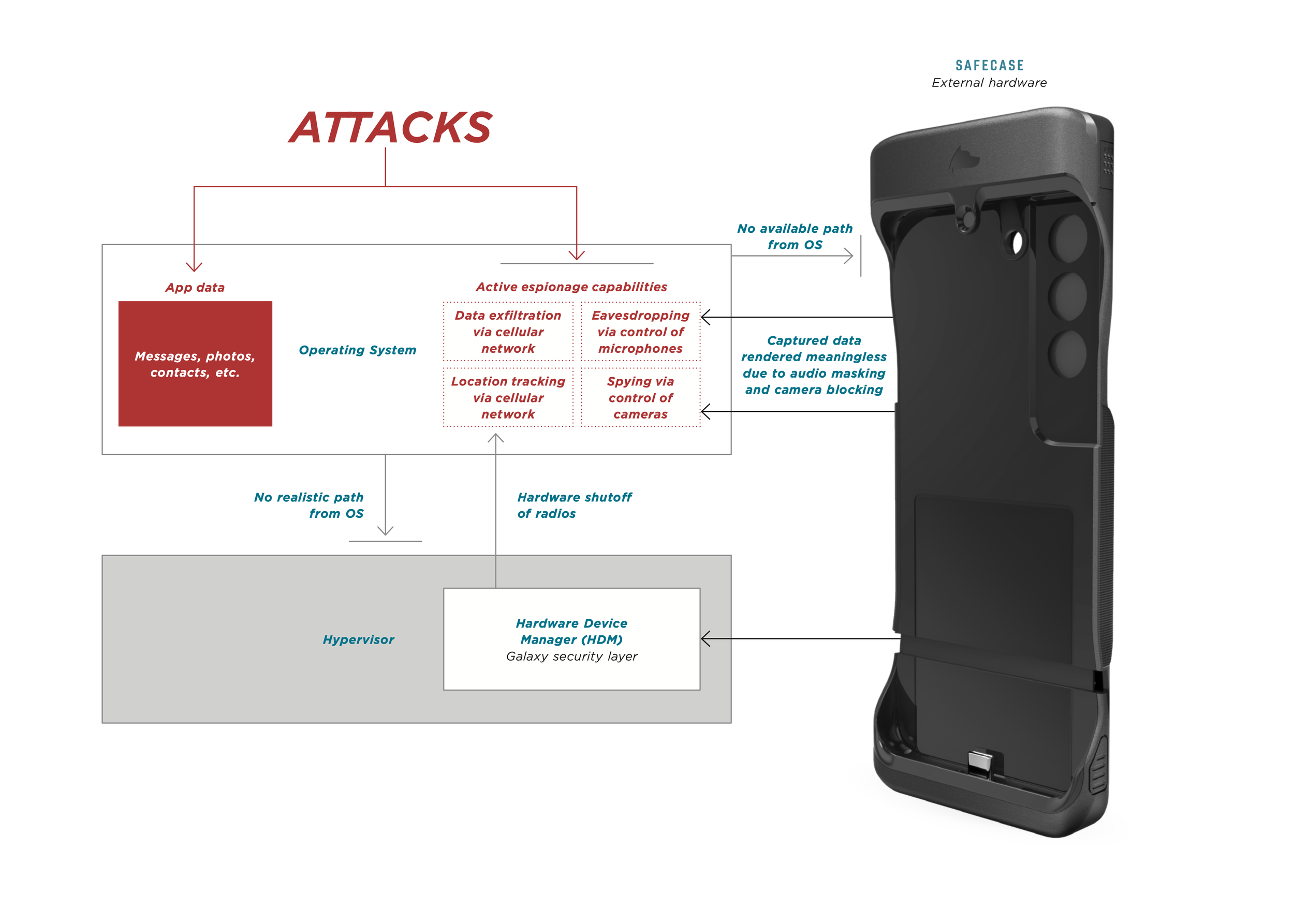
Leveraging phone-independent hardware, SafeCase offers unmatched mitigations against advanced mobile threats.

Meet SafeCase
SafeCase is a specialized, high-assurance computer and security device designed as a discrete phone case.
Phone-independent
Unlike software-based security tools, SafeCase is functionally independent of the reinforced phone. Because it can’t be readily accessed by threat actors, SafeCase continues to deliver protections even if the phone has been compromised.
Improved user confidence
SafeCase is designed and built to withstand nation-state attacks. Anchored on a hardware root of trust, SafeCase limits interaction to only approved, vetted, and signed software, in effect eliminating the risk of core system software being exploited.
Monitorable
In an enterprise setting, SafeCase can be monitored – via the Fulcrum Portal or an existing SIEM – for compliance with phone policies. Optional MDM/EMM integrations enable enforcement directly on a user’s phone.
Capabilities
SafeCase is available in three models, each offering a set of protections against mobile surveillance and/or tracking and hacking.

SafeCase CRBN™ (Carbon)
-
Audio masking and camera blocking
-
N/A
-
iPhone 15
iPhone 12

SafeCase CRBN X™ (Carbon X)
-
Audio masking and camera blocking
-
Secure, chip-level control of phone radios (via HDM)
-
Galaxy S23
Galaxy S22

SafeCase ONX™ (Onyx)
-
Secure, chip-level control of phone cameras/microphones (via HDM)
-
Secure, chip-level control of phone radios (via HDM)
-
Galaxy S23
HDM Integration for Trusted Control of Phone Hardware

A unique hardware-to-hardware integration between SafeCase and flagship Samsung phones – starting with Galaxy S23 – enables SafeCase to provide secure, chip-level control over the phone’s radios (cellular/GPS, WiFi, Bluetooth and NFC) and A/V (cameras and microphones). Even if the phone has been compromised, the user can be sure that selected hardware components are truly disabled and thus unavailable to attackers looking to track and surveil. Go deeper >

Fulcrum is a cloud-based service enabling management, monitoring and control of an organization’s SafeCase fleet. Crucially, Fulcrum enables administrators to establish policies around SafeCase usage and to be notified of policy violations. An optional integration with the organization’s device management system (MDM or EMM) enables enforcement actions directly on a user’s phone. Go deeper >

Fulcrum for SafeCase Management, Monitoring and Control

Get started — schedule your demonstration
Our product demonstration calls cover the following:
Understanding your secure mobility needs
Privoro solution certifications and approvals, and current customers
Implementation requirements for onboarding the Privoro solution
A demonstration of Privoro capabilities
Privoro needs the contact information you provide to enable direct communication with you about our products and services. You may unsubscribe from these communications anytime. For information on how to unsubscribe, as well as our privacy practices and commitment to protecting your privacy, see our Privacy Policy.